Google Cloud has published its latest Threat Horizons Report containing recommendations on improving cloud security and mitigating risks amidst digital transformation.
Addressing emerging threats
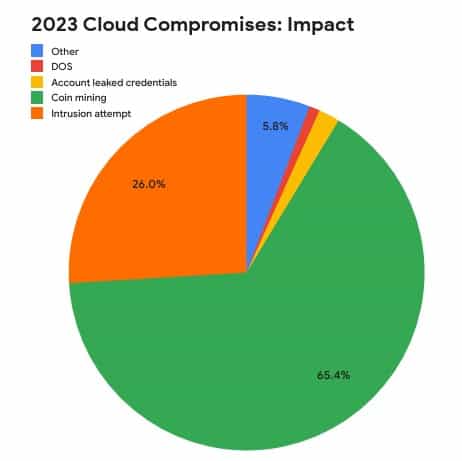
The report reveals that the top cloud security concerns in 2024 are credential abuse, crypto mining, ransomware, and data theft. As cloud environments evolve, malicious players target victims with weak passwords and misconfigurations. Cryptomining ransomware attacks and data theft pose significant security risks and possible data loss.
According to the report, attacks have become more sophisticated by manipulating and deleting security event logs to evade detection, highlighting the importance of security event logging and implementing stringent access controls to protect sensitive data.
Defense against security threats
The Threat Horizons Report recommends strengthening security measures such as two-factor authentication (2FA), strong password policies, identity access and management (IAM) policies, Cloud Audit Logs, and Security Command Centre.
Moreover, unprotected cloud storage services and misconfigured networks continue to become targets of ransomware attacks and data theft incidents. Google Cloud recommends strengthening cloud asset management and data protection. System compromises through weak credentials, misconfigurations, application vulnerabilities, and third-party issues heighten the need for comprehensive security measures.
Proactive measures and awareness:
As malicious players exploit vulnerabilities in cloud environments, Google Cloud recommends risk mitigation, including regular security assessments, employee training, and adherence to best practices.
With the inevitable evolution of cloud environments and attack strategies, organisations should strengthen their cyber resilience against evolving threats through proactive security measures and growing knowledge on emerging threats.





